| View unanswered posts | View active topics |
It is currently Tue Jul 01, 2025 1:48 am |
|
All times are UTC |
|
|
Page 4 of 9 |
[ 180 posts ] | Go to page Previous 1, 2, 3, 4, 5, 6, 7 ... 9 Next |
| Print view | Previous topic | Next topic |
No longer laughable...(Texas Toast's Shiplog)
| Author | Message |
|---|---|
 Joined: Mon Sep 08, 2014 6:44 pm Posts: 847 |
I didn't do a whole lot during the Bane event. I was really busy outside the game, making it less of a priority, and then we had a tropical storm come through and knock out all of the power in my area for the last few days of the event. I did manage to get and upgrade a pair of carapace at least. I also got a pair of terrorcharged emitters, 43 psybeacons, 3 psyshade arsenals. I'll try to do a little hunting before the bane actually get turned off to use my last couple of psyshade inducers.
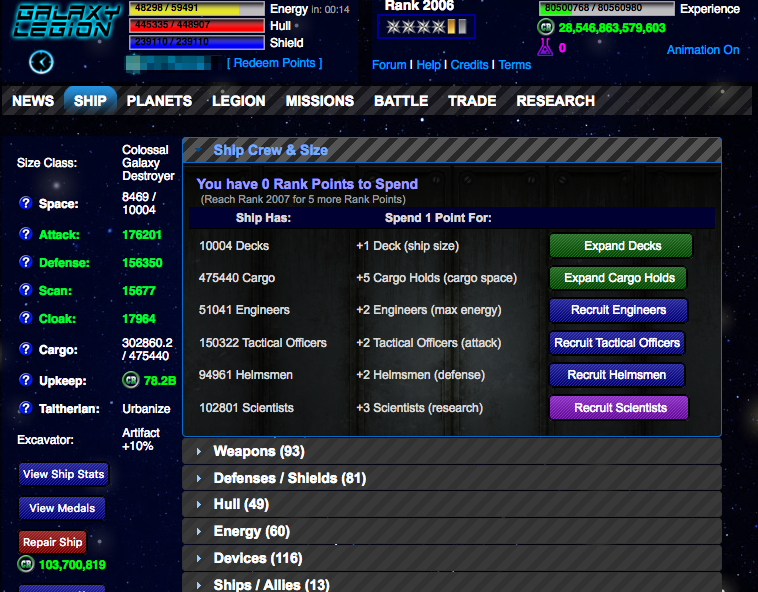
I was also able to get both the Living Nightmare and Fire and Brimstone medals. Not going to bother with the Enveloping Villainy medal, and I didn't spend much time working towards Bag of Tricks. I got 7 out of 12 professions just by setting traps as I found them, but since I didn't do much NPCing I didn't really find many traps (and most phantoms were turned into psyshades when possible.) I'm way behind turning in artifacts and rank points; I've got triple digits on hand of all of the androids and prisoners etc. But, with where I'm at turning things in now:  So, only 26 ranks. Solynia is now up to rank 37. All rank points have been going into TACOs, which went up around 3k. 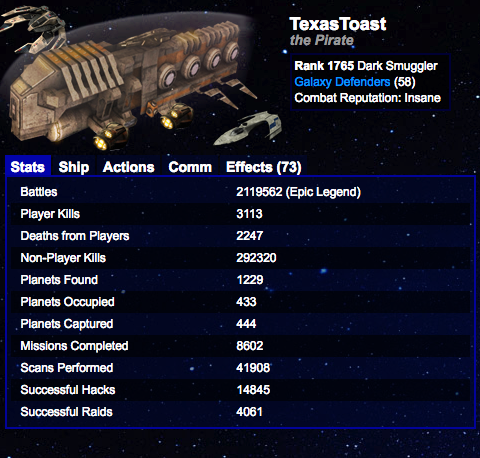 I've got 9 or 10 open planet slots, depending on if the drannik colonization bug thing actually got fixed. Haven't gotten near my limit yet to test that out. I'll be colonizing again once the Harvest starts, as I have mostly been waiting to colonize more in case of new medals or if there are some medals I don't have yet. Too lazy to look, but I think there is one. I'm now at 2610 medal points, and have less than 1000 raids to go to get the last raiding medal. My only PvP medals remaining are that and Exotica.  I have moved up 3 more spots on the hacks leaderboard. That's been helped along a bit by having the extra time manipulator actions finally. Minerals 132199 units / hour (4.3 hours) Artifacts 153736 points / hour (4.9 hours) Research 161627 research / hour (3.8 hours) Again, no real change in production as I haven't added a ton of new planets. Will be nice once Solynia is fully ranked and I can go back to invading everything again. _________________ --------------- GD: A good legion for collecting relic badges --------------- --------------------------------------------------------------------- |
| Wed Nov 01, 2017 3:44 pm |
|
 Joined: Mon Sep 08, 2014 6:44 pm Posts: 847 |
I did not do nearly as much NPCing as I'd hoped to do during the Harvest event, so not many terrafounders collected. Oh well, I got to colonize a bunch of planets, so Solynia is now rank 47. I contributed over a million energy towards our base upgrade, which was a bit shy of a quarter of all energy donations this past month. I also got the Terran Nature, Habitable Harvest, and Nature's Protection medals, leaving me at 2640 of 3520 medal points right now.
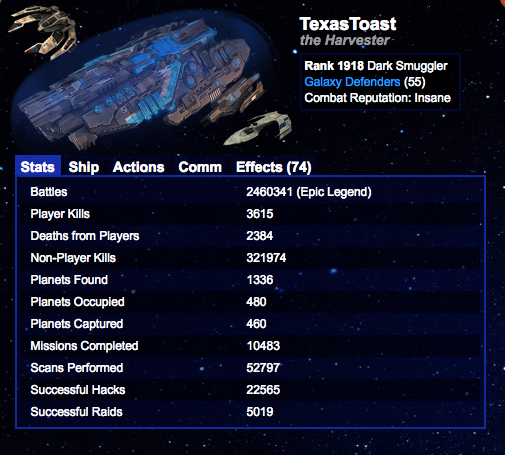
Here are my current stats:  Gained 41 ranks, around 7500 TACOs, and even more rank points needing to be turned in. I have also hit over 6 digits by default with no temporary buffs when attacking NPCs, which is nice. 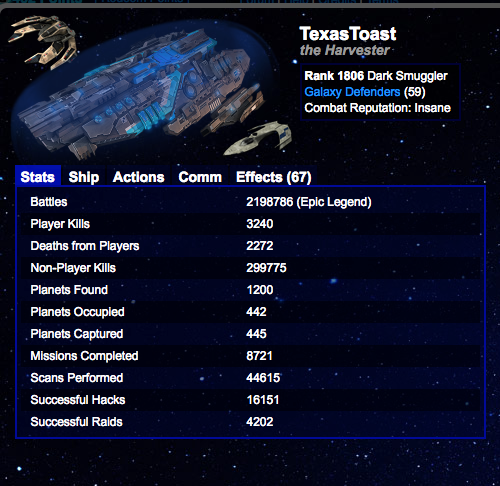 I'm at 10 or 11 open planet slots, so basically treaded water with colonizing while ranking throughout the month. Less than 800 raids to go for the last raiding medal, and now moved 4 more slots up the hacks leaderboard.  Per the recent post here in the forums asking for better badge messages, I've been picking a lame joke of the day to leave on folks comms if I disable them. That's been fun. Not a huge change in production, though I'm not running all my buffs right now. I am usually in the 160s for artifacts per hour. Minerals 130572 units / hour (4.4 hours) Artifacts 156120 points / hour (4.9 hours) Research 162147 research / hour (3.8 hours) _________________ --------------- GD: A good legion for collecting relic badges --------------- --------------------------------------------------------------------- |
| Sat Dec 02, 2017 6:26 pm |
|
 Joined: Mon Sep 08, 2014 6:44 pm Posts: 847 |
Post-Scruuge update!
Once again, was very busy and actually did a lot less NPCing than I had planned on. Oh well. I did get my Hullbuster Sale and Presents and Future medals, bringing me to 2660 of 3540. I've got 39 resupply depots in my cargo, and placed somewhere around 6-8 of them on planets already, I think. Wound up with 3 gift of the void, 2 gift of the stars, and 1 gift of the ancients; as I said, not much NPCing. Over 80 gift to the naughty left, which is about how many I had going into the event, so despite handing a lot out the first week and a half, I merely replaced what I used. Current stats: 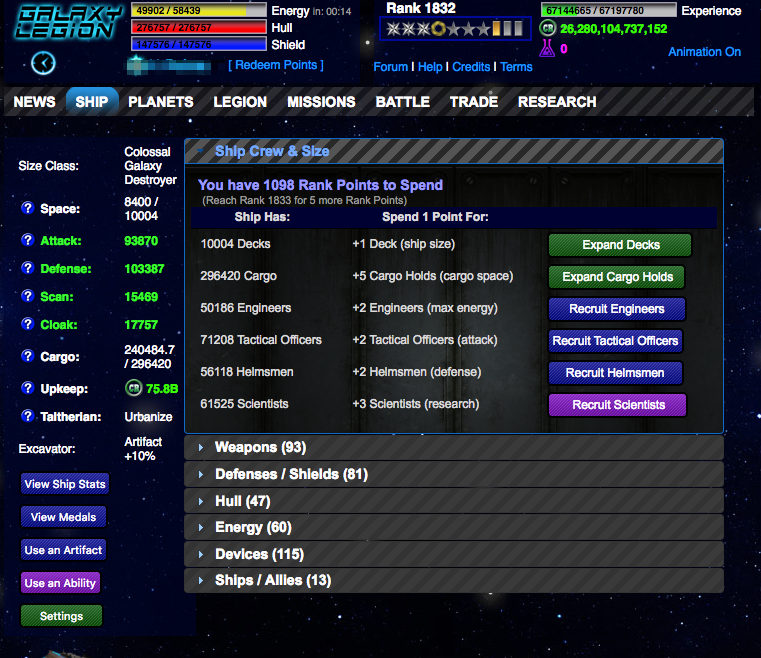 Only 26 ranks, which is less than 1 per day. Definitely a slowdown for me. Will be concentrating on base donations for the next month I guess, since I don't plan to do a ton of NPCing until Q-Pedd unless I get a legion mission that calls for it. I did catch up on my rank points, briefly, but as you can tell I'm way behind again (though I did turn in over 500 of them over the last day or two...of course, haven't turned in rescued prisoners in that time either though...) Over 5000 more TACOs for the month, with a few thousand more to be coming in the very near future once I can get around to doing a lot of clicking. Maybe I'll have to watch some videos for work and can sit there giving myself carpal tunnel... 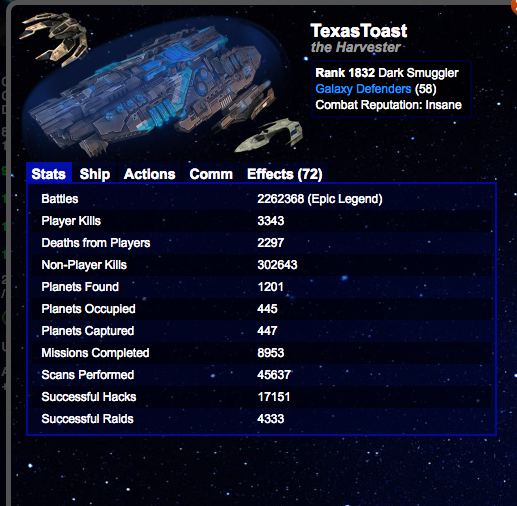 I'm now up to 14 or 15 empty planet slots, depending on the drannik colony fix. I really need to get off my butt and colonize a few more planets. 667 raids to go to get the last raiding medal, so I should make progress on that this month. I took the last week and a half off of PvP as I was just too busy, which meant folks had to deal with a Holiday Hiatus of my Bad Joke Badge Comms, which seem to be oddly polarizing. Most folks that respond to them seem to appreciate them, but a few people get mad at me for them. Which seems silly. I'm now comm blocked on a lot of people's comms, and one player specifically that doesn't like being hacked managed to goad me into zeroing him by using a bunch of TiBs on me so he's actually blocked me. I am looking forward to that wearing off, because it's put him on my permanent special attention list rather than just being another random person on my battle tab. Speaking of, my strategy of PvPing until my time manipulators stop working once per day 4-5 times per week works out pretty well. I did get as high as 12th on the hacks leaderboard, but a week and a half off has actually dropped me a spot compared to last month:  i think I can get close to if not in the top 10 by the end of January though for my next update. We'll see. Either way, I'll be collecting a lot of badges which is the important thing. (I actually ran out of reds this weekend from locking bases.) Minerals 142788 units / hour (4.1 hours) Artifacts 170035 points / hour (5.2 hours) Research 170468 research / hour (3.6 hours) Production is slowly creeping up and I'll shortly be passing my research production with artifact production (finally) so that will be nice. With hyperturbines on over 50 of my planets, I've slowed down placing those and am concentrating a bit on adding storage capacity so that I don't lose quite as much production overnight. Only aiming at hyperturbines for new planets that already have over 1k artifact production going forward. If I could invade to fill my planet slots I'd be able to get up to 200k/hour I think without too much trouble...but finding colonizable planets for Solynia is proving to be a drag. Only rank 51 so far, so 49 to go. _________________ --------------- GD: A good legion for collecting relic badges --------------- --------------------------------------------------------------------- |
| Mon Jan 01, 2018 3:32 pm |
|
 Joined: Mon Sep 08, 2014 6:44 pm Posts: 847 |
Q-Pedd is about to start, so going a day early this month.
This month I did wind up doing a little more NPCing than I have been during the seasonals, at least subjectively (I haven't actually compared the NPC kill totals.) Hoping to spend more time NPCing and collecting terraforming devices during Q-Pedd since I'm running low on them now. I am up to 2675 medal points, and finally got the Firewall medal! 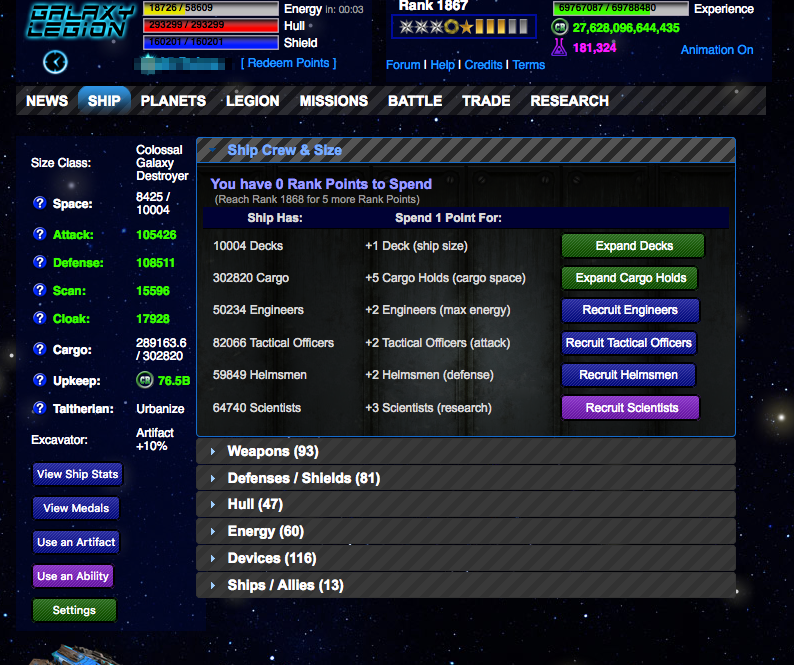 35 ranks this month, and about 10k TACOs, so some good progress on that front. I think I'm at the point that I'm still 6 digit NPC attack debuffed from a DCN or hypergrid but without any temporary buffs. Was really close a couple days ago and worked through my rank points since then. I've been making good progress with Solynia, who is now at rank 81. A legionmate went traveling and has been sharing the planets of mine she has on scan to try and free up planet slots for me. 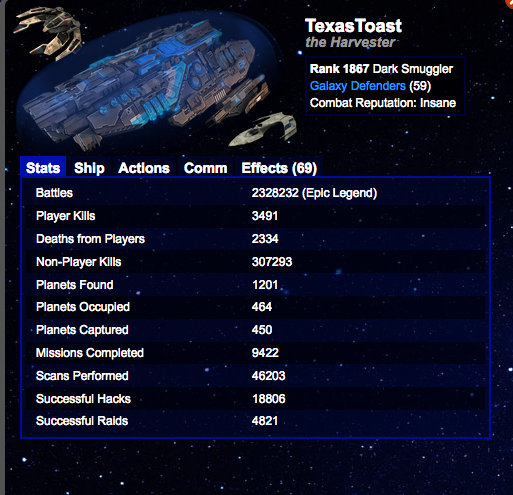 I have actually filled my planet slots a few times, though currently I've got a few available. I also passed Peticks (briefly) on the hacks leaderboard, but he took advantage of my not doing much on weekends to rebuild a lead.  Still not top 10, but it's a moving target and will get there eventually, I expect. Minerals 148872 units / hour (4.1 hours) Artifacts 188622 points / hour (5.3 hours) Research 183328 research / hour (3.4 hours) Production is creeping up. Small gains in mining and research, large gains in artifacts. I've been converting some of my plasmas to artifact planets and making them a bit more useful, and a renewed interest in polychoron vaults has been helping to maintain my capacity so I lose less over night. _________________ --------------- GD: A good legion for collecting relic badges --------------- --------------------------------------------------------------------- |
| Wed Jan 31, 2018 1:40 pm |
|
 Joined: Mon Sep 08, 2014 6:44 pm Posts: 847 |
Coming off of a week long trip across the country to a mastermind and conference, so pretty exhausted, so I'm going to just drop some numbers and not put a lot of thought behind this month's update.
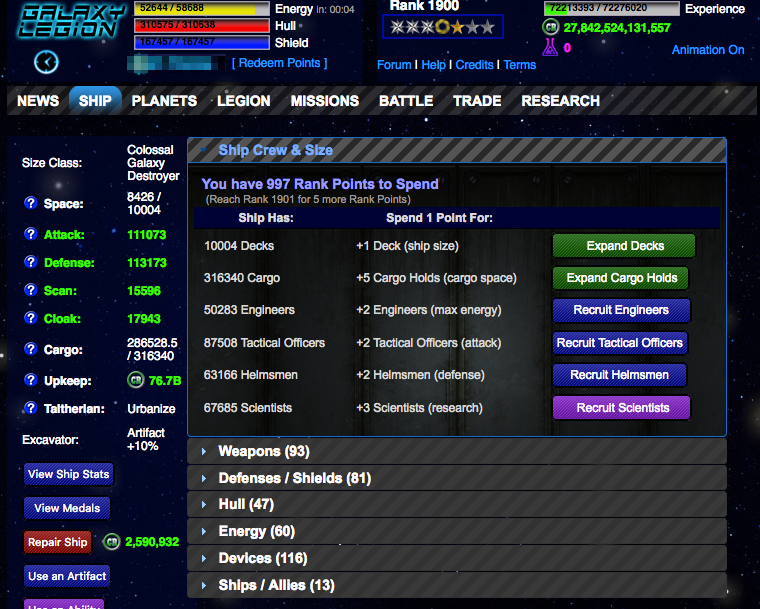 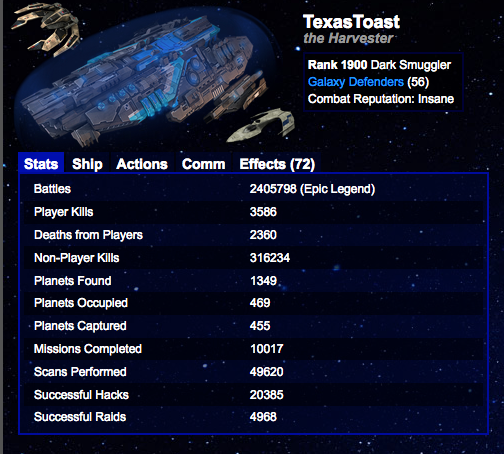 Main relevant note not seen in the screenshots is that I have 6 open planet slots and need 11 ranks for Solynia. That will happen this month some time, hopefully earlier rather than later. Shouldn't be hard once Lepus starts.  I did pass Peticks a few times, but taking a week off from hacks means he passed me again. He has moved over to my legion so I can't hack him anymore, unfortunately. Top 10 is always a moving target, but I think it's possible to hit that by my next update or two if I can find the time to be diligent. Minerals 148027 units / hour (4.2 hours) Artifacts 188749 points / hour (5.4 hours) Research 178332 research / hour (3.7 hours) Production actually creeped down a little. I did lose a couple planets this month, but mostly I don't have all my buffs running right now for the last week so that's probably what hit the minerals/artifacts the most, once I buff up they'll be a bit higher. My capacity has improved, if not a huge amount in production. For research, I've been converting those to artifact planets, so I expect that that'll mostly maintain from what I get in scientists. Of which I have a few hundred to use... _________________ --------------- GD: A good legion for collecting relic badges --------------- --------------------------------------------------------------------- |
| Thu Mar 01, 2018 2:49 pm |
|
 Joined: Mon Sep 08, 2014 6:44 pm Posts: 847 |
Finished ranking Solynia. Made top 10 in hacks (but not quite above the fold, one more spot to go there.) Nothing else to really report on; had a 3 day migraine morph into the flu this week so haven't been active. Switched away from being talth excavator, so production took a hit, but was able to put aerlen patronage on my rift. Once I get a gateway link then I'll go back to talth excavator but who knows how long that will take. Might give up and swtich back before then.
   Minerals 144862 units / hour (4.7 hours) Artifacts 174276 points / hour (6.2 hours) Research 177273 research / hour (4.0 hours) _________________ --------------- GD: A good legion for collecting relic badges --------------- --------------------------------------------------------------------- |
| Sun Apr 01, 2018 12:11 pm |
|
 Joined: Mon Sep 08, 2014 6:44 pm Posts: 847 |
Last month I did a little digging around my planets and figured out what I actually had, forgot to add this to yesterday's update. (I blame the flu.)
Best resource on the planets: Code: Artifact Planets: 289 60.08% Mining Planets: 120 24.95% Research Planets: 72 14.97% Storage Planets: 0 0.00% Actual production type based on what the planet is actively producing: Code: Artifact Planets: 315 65.49% Mining Planets: 124 25.78% Research Planets: 36 7.48% Storage Planets: 6 1.25% I'm in the process of converting my biggest research planets (especially ones w/effects) into artifact planets, so that's been helpful. _________________ --------------- GD: A good legion for collecting relic badges --------------- --------------------------------------------------------------------- |
| Mon Apr 02, 2018 3:38 pm |
|
|
Joined: Sat Oct 15, 2011 5:09 am Posts: 3473 |
Texas Toast wrote: Actual production type based on what the planet is actively producing: Code: Artifact Planets: 315 65.49% Mining Planets: 124 25.78% Research Planets: 36 7.48% Storage Planets: 6 1.25% i think this is pretty interesting info. here are my stats for comparison: Code: Artifact Planets: 422 82.6% - minimum 275 arti per hour Mining Planets: 49 9.6% - minimum 924 mining per hour (being boosted .. next lowest is 975 mining per hour) Research Planets: 0 00% Storage Planets: 35 6.8% - C plasmas collect a bit of research; VM metallics a bit of mining Miscellaneous Planets: 5 1.0% - recently invaded (to be abandoned) / futbawls time to cap production: artifact: 5.87 hours mining: 7.58 hours research: 3.92 hours _________________ Rank 3950 Litheor Governor 100% DCR r385-r2200 GL Marauder #26 _____________  PvP leaderboards: 70212 raids: #1; 40852 kills: #1; 96377 hacks: #3; |
| Mon Apr 02, 2018 4:52 pm |
|
 Joined: Mon Sep 08, 2014 6:44 pm Posts: 847 |
Above the fold!
 Only by 6 hacks, will likely lose it over the weekend, but should regain it without much trouble before my next actual update. But, hey, finally above the fold. _________________ --------------- GD: A good legion for collecting relic badges --------------- --------------------------------------------------------------------- |
| Fri Apr 20, 2018 5:36 pm |
|
 Joined: Mon Sep 08, 2014 6:44 pm Posts: 847 |
Biggest news was getting above the fold a week and a half ago, and am now comfortably in position #8 on the hacks leaderboard. Still aerlen fixer; no ardyne sabotage yet. Will probably give up waiting soon and just get it next year at some point if I'm still playing.
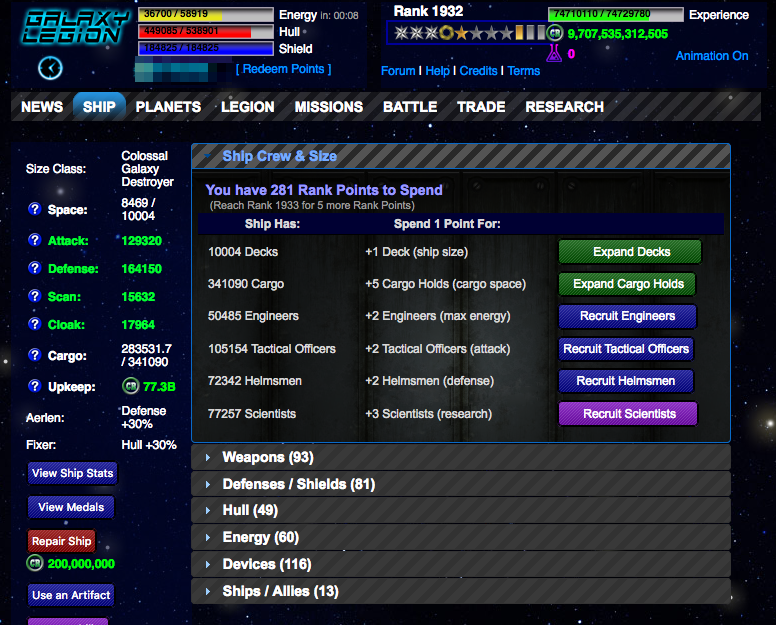 Crossed 6 digits on the TACOs. Maxed my cobalt drive, so energy is going up a wee bit on a daily basis. Still going all rank points to tacos at this point. Not sure if/when I'll put any back into engineers, but no real plans right now to. Note that I added the droid maintenance this morning, so go off the current hull rather than max hull in the screenshot. 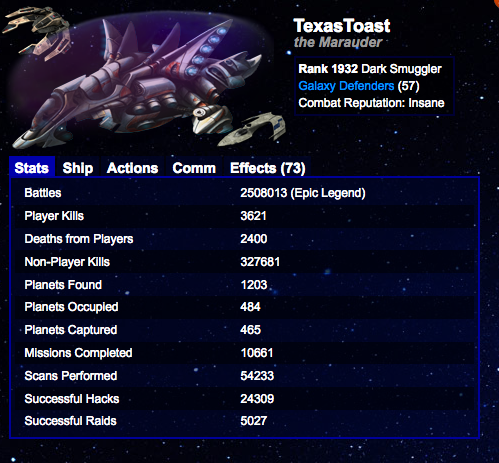 I've been keeping my planet slots full; looking forward to going back to excavator as a profession. Minerals 149075 units / hour (4.7 hours) Artifacts 184959 points / hour (6.0 hours) Research 189407 research / hour (3.8 hours) 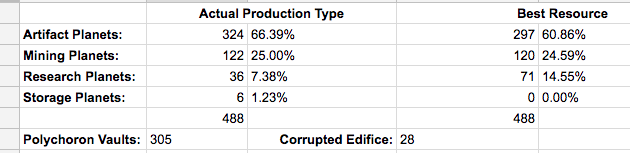 Unbuffed vs NPCs: Attack: 149704 / Defense: 211676 and in PvP: Attack: 138502 / Defense: 164150 _________________ --------------- GD: A good legion for collecting relic badges --------------- --------------------------------------------------------------------- |
| Tue May 01, 2018 12:29 pm |
|
 Joined: Mon Sep 08, 2014 6:44 pm Posts: 847 |
Not a lot I can think of worth mentioning for the past month personally as it relates to the game. Kinda boring right now w/a long wait between seasonals and nothing new coming.
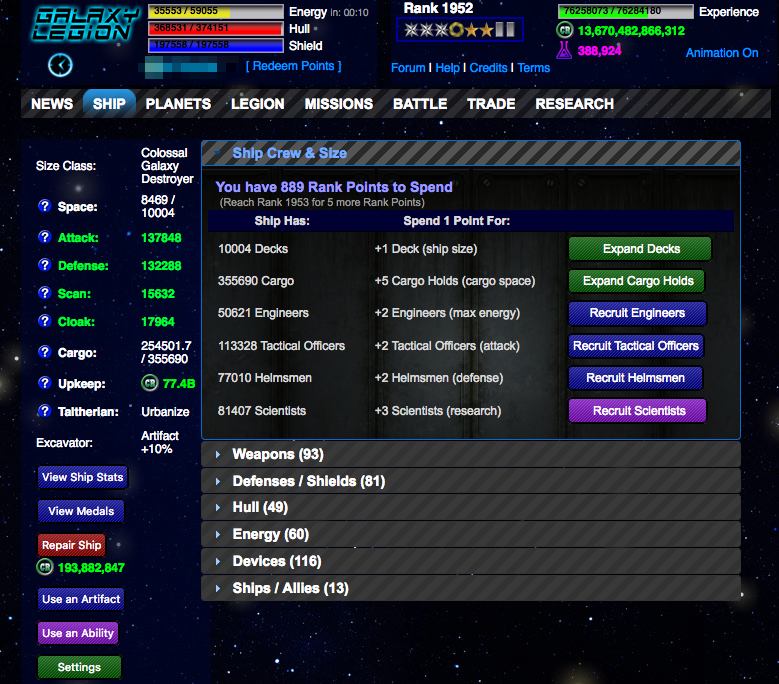 No change in strategy. Rank points are still all going to TACOs these days. Will be losing a bunch of bosses and elites pretty soon. I am guessing they'll last until Elios and disappear at some point then. 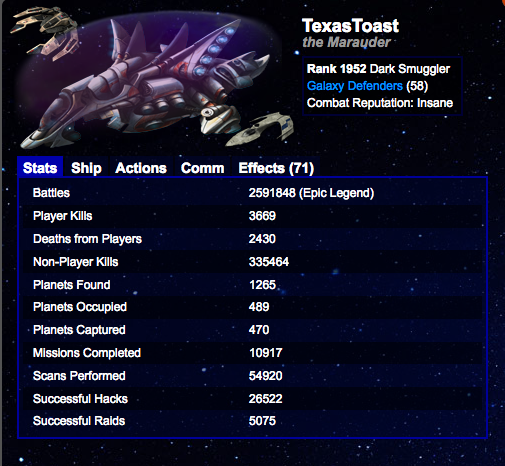 Looks like my kill/deaths ratio stepped back a tiny bit, despite getting foundry of war twice in a row. My "hack first, disable infrequently" mantra is a lot less work, so I doubt I'll change it. No risk of losing my Insane combat reputation, and even if I did, it doesn't really mean much these days.  Moved up a slot to #7 on the hacks leaderboard. Not sure if I'll make #6 or not this month. Potentially. Minerals 151427 units / hour (4.9 hours) Artifacts 210564 points / hour (5.7 hours) Research 191301 research / hour (4.1 hours) Back to being excavator, but not running most of my buffs since AP/hour is a bit lower than I usually am running at. Will have to go through and put those on shortly. Managed to finish a few projects now that I'm Taltherian again as well. 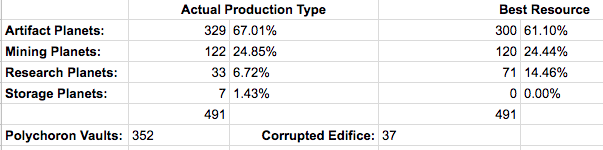 Went through and found a few planets I've lost along the way that were still counted last month, plus added my new planets other than an invasion from a day or two ago, so besides that one missing planet the numbers are accurate. Unbuffed vs NPCs: Attack: 159576 / Defense: 170589 and in PvP: Attack: 147635 / Defense: 132288 Attack is up, defense is down a bit now that I'm no longer an Aerlen. Got a bunch of helmsman I'm behind on turning in as well. _________________ --------------- GD: A good legion for collecting relic badges --------------- --------------------------------------------------------------------- |
| Fri Jun 01, 2018 4:16 pm |
|
 Joined: Mon Sep 08, 2014 6:44 pm Posts: 847 |
Going a little early for this month's update as I've gotten tired of an asshat TiBing me so he can disable me and have started returning the favor, and expect that I'll spend the next few days with a lot of buffs on constantly as I've already been alerted because poor whiny boy got his feelings hurt. (I assume that's the case; he hasn't tried comming me at all. Last time we went through this, he comm blocked me after I pointed out he should stop being a baby when all I did in return was zero his hacks and that he is welcome to zero my hacks or even disable raid me as long as he doesn't mind me hacking him back. But apparently, that wasn't allowed, and the TiBs sure are annoying. I've got 15,000 blue badges or so however, so I won't run out any time soon.)
Looking forward to Elios...another week and a half or so.  Still sending all of my rank points into TACOs. Added about 10k since the last update, though not really noticing much of a difference in general and thinking that going for helmsman might be the way to go...added about 4k just from using androids and ship modules, so could easily triple that. 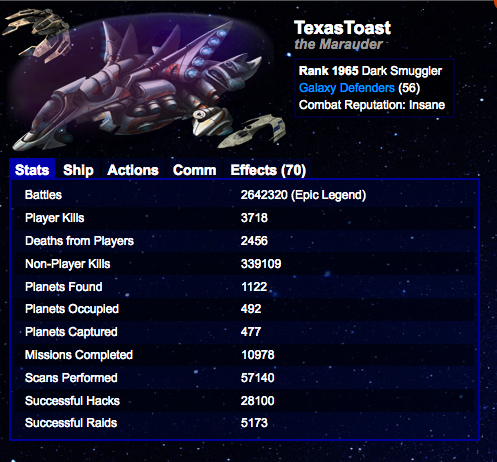 I've been keeping my planet slots full without too much difficulty, dropped a few dud planets along the way and improving other planets. Made myself a new MC oceanic. About 100 raids and 50 disables and half that in deaths so ratios are all working out all right. Added about 1500 hacks, mostly PvPing during the week and taking weekends off. No change in the leaderboard position:  I'm less than 800 hacks behind CapitainePaul now, who only added about 600 hacks in the last few weeks. I expect, barring any sudden new activity, that I'll catch CP in the next week or two, and depending on how things go with the asshats and how many TM actions I waste on them I could potentially catch Crack Fox (who only hacked 8 times this month) though I expect that'll happen in August. I don't expect to move much higher than #5 this year, which likely means that'll be as high as I get. Minerals 158573 units / hour (4.9 hours) Artifacts 223348 points / hour (5.6 hours) Research 209164 research / hour (3.8 hours) Production is moving in the right direction a little quicker. Just hit my 4 year anniversary and got my throne of reverence for the rift. That'll help things out a bit. Usually range between 220k-225k arti per hour. Once Elios gets here, will be doing a ton of NPCing so that I can replenish my depleted stock of terraforming devices and will finish off a bunch of my project planets. I'm really close to losing DCNs and Hypergrids and other lower rank bosses and elites that drop a lot of CTP-scrappable items, and then the troop carriers a few hundred ranks behind that, so I'm going to see how close to losing troop carriers I can get during Elios. 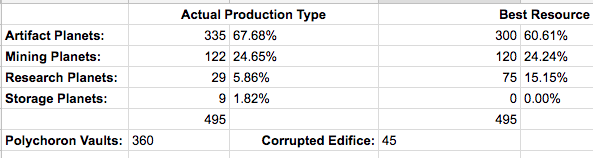 That list is almost up to date, got one planet that hasn't gotten on the list yet, but it's just a 300 or 400 arti producer, not much of note on it. Unbuffed vs NPCs: Attack: 171867 / Defense: 177980 and in PvP: Attack: 159006 / Defense: 138019 About where I'd expect to be for attack and defense. Caught up on turning in helmsmen and the like. _________________ --------------- GD: A good legion for collecting relic badges --------------- --------------------------------------------------------------------- |
| Thu Jun 28, 2018 3:19 pm |
|
 Joined: Mon Sep 08, 2014 6:44 pm Posts: 847 |
Coming in a day early this month now that Elios is done. Looks like I gained 28 ranks by killing 16,984 NPCs and came through Elios with a net gain of 3928 actual CTP and 7225-14566 of scrappable CTP. So not as much as I'd thought, but I had a couple of really busy weeks (it is Summer and I do have 2 kids...) so didn't get quite as much NPCing in as I wanted to.
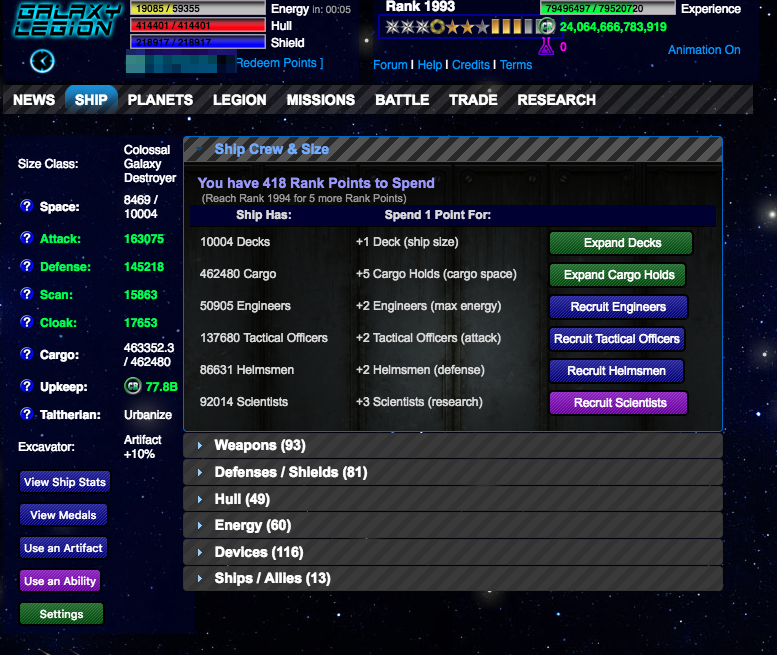 Some good progress this month with 14k TACOs added and about 7k base defense. My scan/cloak will swap a bit next week as I put my Composite Rays back in order; I had the scanners installed for Elios and if we succeed in the current legion mission will have a scanning task for the next one. Only 8 ranks away from losing a bunch of elites and bosses, and then another 200 ranks after that I'll lose my troop carriers. 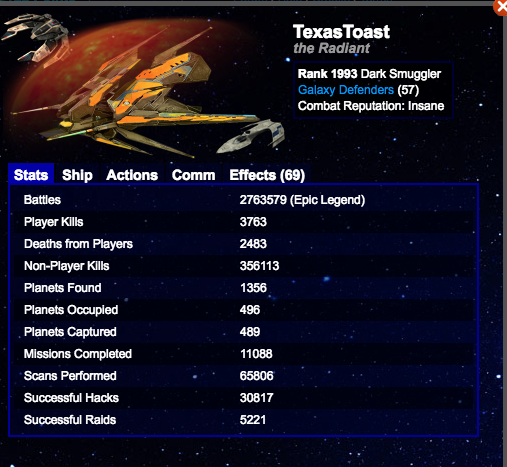 I've actually been doing a great job of adding new planets lately (including a natty dyson!) with 12 invasions, but actually lost quite a few during the scan fest of Elios as well. (I abandoned some of my junk along the way also.) So I have 3 open slots right now with a few more opening up soon.  I've gotten into a good groove with my hacking. Over 2700 hacks in the past month, moving 2 spots up the leaderboard to #5. It'll be a bit of a slog to catch Pac Man. Minerals 166703 units / hour (5.4 hours) Artifacts 239411 points / hour (5.6 hours) Research 216280 research / hour (4.0 hours) Not many if any production buffs on right now; I've actually been running around 250k+ arti/hour lately, helped by the new dyson. (An active player had it on scans, too, which surprised me it was available.) Production storage has improved quite a lot as well, thanks to placing all of my powervaults and upgrading a bunch I found that hadn't been in the process, as well as getting the vast majority of my planets to have a polychoron vault and/or corrupted edifice. (Only around 30 planets now that don't have at least one if not both of them.) 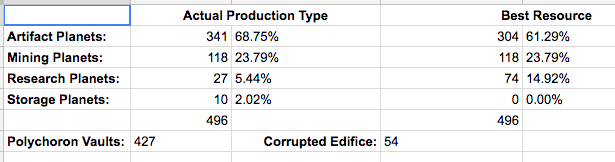 Unbuffed vs NPCs: Attack: 188780 / Defense: 187263 and in PvP: Attack: 174653 / Defense: 145218 _________________ --------------- GD: A good legion for collecting relic badges --------------- --------------------------------------------------------------------- |
| Tue Jul 31, 2018 11:41 am |
|
 Joined: Mon Sep 08, 2014 6:44 pm Posts: 847 |
1 day early, figured my warp fuel wore off so would grab a record now as who knows if I'll be on tomorrow.
 Added over 13k TACOs to pass 150k (this morning!) and added 11k base defense. I lost a bunch of elites and bosses now that I've rolled past rank 2001. Slow ranking those last 5 or 6 ranks was really boring; I don't know how folks slow or freeze rank. Been busy this week so haven't advanced too far past there, but Chuhn starts in less than a week (most likely) so will get plenty of NPCing in soon enough. Alerts come in much less frequently now. 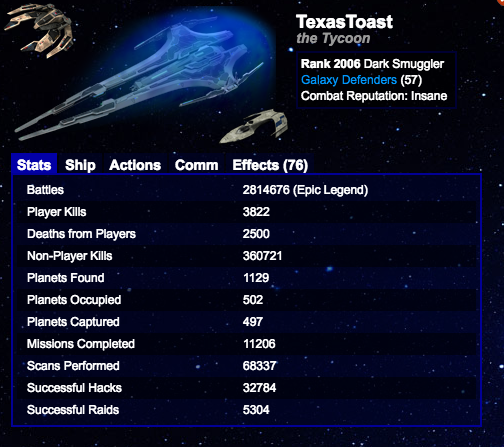 I've been abandoning some of my junk planets, haven't really lost too many more since Elios. I had an excellent scan run a few days ago that got me a fully kitted storage planet and a nice 20x VM planet, plus a couple from actives that I have yet to invade once I get my next VoCs. I also picked up a crappy desert planet that had a bunch of storage artifacts on it that I'll be stripping and abandoning once I collect the build extractors so I can move those to better planets for them. Only about 4k NPC kills this month, given that I was trying to slow rank and hit as many alerted bosses and elites as I could before I lost 'em. Just shy of 2k hacks this month, averaging 63/day through the month. Most weeks I got at least 4 days of maxing my actions, though that total was half again as high for July so I'll need to pick up a little slack... I have gotten some complaints about my Bad Joke Badge Comms...but nowhere near as many as I get compliments for them. So they won't stop. If you don't like them, then block my comms or delete them. If you do block my comms, though, don't whine like a little baby if I crit-hack a planet from you and don't tell you which one it is...I hack 100-125 people a day in about 30-40 minutes and get 6-7 crit-hacks every day on average (unless I forget my scan buffs, in which case I usually get counter-crit-hacked that many times...) Especially as in the case a couple days ago where I did a scan run before my PvP run, I'm not going to have any idea if I can't leave a comm message right then and there to tell you which planet I got (and if it's enemy occupied, most likely purged already anyway.)  No changes for me on the hacks leaderboard (congrats to CapitainePaul for passing The Crack Fox for #6) though I did have about 1500 more hacks than Pac Man and now trail him by 1268 hacks. I expect I'll pass him within my next update or two. I don't think CP will catch me any time soon since I doubled my lead over him this past month. Minerals 169519 units / hour (5.7 hours) Artifacts 249078 points / hour (5.8 hours) Research 228453 research / hour (4.0 hours) Not sure where my production buffs are right now, I think a bunch are going but definitely not all of them. Still hanging around the 250-260k range most of the time. I do have a couple dud planets production wise with my new storage planet and crap that just happens to have some storage on it right now. I've been doing a good job of adding polychoron vaults to everything, which has made a huge difference in what I can collect overnight at the expense of (mostly) just a few artifact points per hour when I'm online. I have been going through and adding planet data optimizers to anything and everything to add to the research as I abandon my research planets, and while trying to clear out cargo I went through my artifact planets to apply gravitic amplifiers as I ran out of fold generators and figured I had hundreds of those sitting around. Basically used 'em on any arti-producing planet VL or larger. I still have a few hundred left. 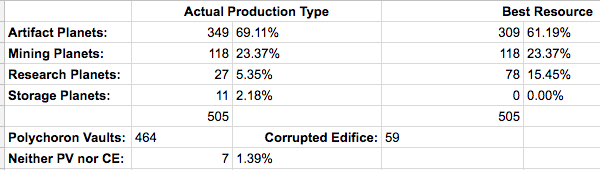 Now up to 464 PVs placed and 59 corrupted edifice. I only have 7 planets that don't have at least one or the other (all of which are high artifact producers) so after Chuhn when I've restored my collection of build extracters a bit I'll start going through and adding them to the lesser-producing planets that have CEs but no PVs and maybe revisit a couple of the planets still lacking a PV. The unfortunate side-effect is that if I do fill my production bar, I'm getting close to needing a third collect-all to actually get my production. Unbuffed vs NPCs: Attack: 203975 / Defense: 201626 and in PvP: Attack: 188711 / Defense: 156356 _________________ --------------- GD: A good legion for collecting relic badges --------------- --------------------------------------------------------------------- |
| Fri Aug 31, 2018 6:49 pm |
|
 Joined: Mon Sep 08, 2014 6:44 pm Posts: 847 |
Chuhn is over. Well, supposedly, hopefully there's a few hours of the traders dropping in the battle tab left before it gets turned off. I had 152,222 initial ctp scrapping at the start of the seasonal, and for the seasonal netted an additional 164,406 ctp over what I started with. Obviously, it costs CTP to trade, and I also used the UST quite a bit throughout the last few weeks, but 12k+ ctp isn't too bad for 3 weeks not including whatever I'd stockpiled ahead of time. I'll take. (Though, most is earmarked for upgrading our base next weekend to level 9...I have enough to level it but letting others get a bit of share in it for our contest and then will finish whatever is left after the contest ends.)
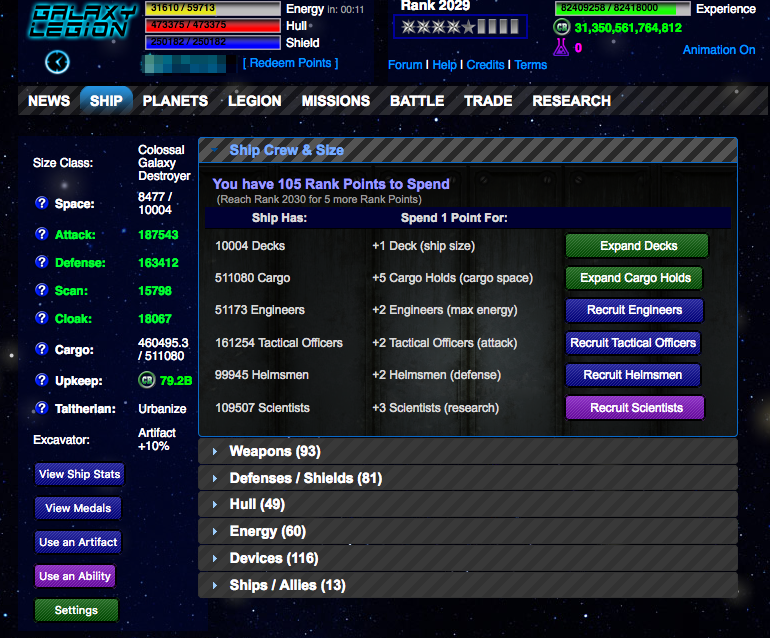 I added about 11k TACOs and and 7k base defense this month, so not quite as much as last month. Losing the elites and bosses at rank 2001 kinda sucks...not nearly as much action in the alerts department, and far less variety when there is. 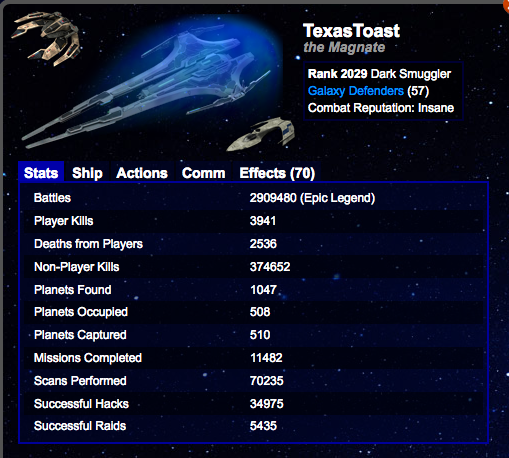 Only 13,931 NPCs killed this month, was really hoping to be 20k+, but it was a really busy month for work so game took second fiddle. Oh well. I added 6 planets, though I had more than twice that in invasions as I've been invading and actually lost a few planets to invasions this month, and made up the rest with abandoning some of my junkier ones. 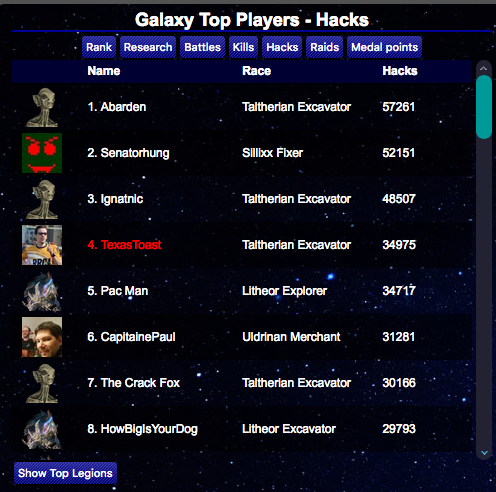 Moved up another slot on the hacks leaderboard to #4, passing Pac Man. He only hacked a little over 900 times, whereas I hacked 2191 times. Ignatic only had 369 hacks last month, so at that rate, and is 13.5k ahead of me, so it's going to take a long time to catch him if I ever do, probably half a year at the current paces, maybe a bit longer. I am hacking more than Abarden and Senatorhung right now, but not enough that I'm likely to catch them within a year, and at this point I would be surprised if I'm still playing at that point. So...we'll see what happens, I guess. But no expectation of advancing any further, though I do expect to maintain my space. Minerals 168244 units / hour (5.8 hours) Artifacts 257194 points / hour (5.8 hours) Research 236568 research / hour (3.9 hours) Not a ton of production buffs running right now, with the Chuhn Prestige I've been running in the 270k-280k range for the most part for the past few weeks. Storage has continued on to be accumulated: 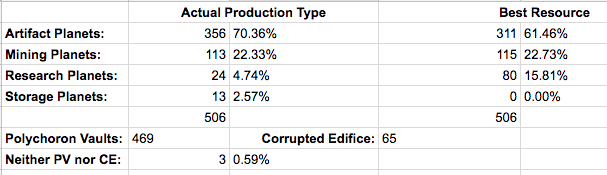 I have 6 planets yet to be recorded and aren't reflected in those numbers, but I've added more polychoron vaults and corrupted edifice and 2 new storage planets. I only have a few planets that don't have at least a PV or CE, and have enough polychoron vaults on hand to get one onto all but my top few producers which I don't want to give up the production for the minimal extra storage. That number without either is unlikely to change going forward. Unbuffed vs NPCS: Attack: 217104 / Defense: 210725 and in PvP: Attack: 200859 / Defense: 163412 _________________ --------------- GD: A good legion for collecting relic badges --------------- --------------------------------------------------------------------- |
| Mon Oct 01, 2018 1:25 pm |
|
|
Joined: Sat Oct 15, 2011 5:09 am Posts: 3473 |
good luck in your effort to catch up to Ignatnic on the hacks leaderboard .. once you get closer he will give you a run for it.
_________________ Rank 3950 Litheor Governor 100% DCR r385-r2200 GL Marauder #26 _____________  PvP leaderboards: 70212 raids: #1; 40852 kills: #1; 96377 hacks: #3; |
| Tue Oct 02, 2018 8:44 am |
|
 Joined: Mon Sep 08, 2014 6:44 pm Posts: 847 |
Galaxys Pub has reached level 9 Base gained +5 Special Size, +10 Standard Size, 5 Production Points, and 4050 Hull/Shield.
_________________ --------------- GD: A good legion for collecting relic badges --------------- --------------------------------------------------------------------- |
| Mon Oct 08, 2018 2:00 am |
|
|
Joined: Tue Aug 16, 2011 3:02 pm Posts: 942 |
Texas Toast wrote: Galaxys Pub has reached level 9 Base gained +5 Special Size, +10 Standard Size, 5 Production Points, and 4050 Hull/Shield. This should be in the "Legion" section of the Forums...unless you financed the entire thing yourself... _________________ As of 08/07/2021 treadmillers will be ZEROED!!! |
| Mon Oct 08, 2018 2:27 am |
|
 Joined: Thu Oct 27, 2016 2:52 pm Posts: 321 |
CapitainePaul wrote: Texas Toast wrote: Galaxys Pub has reached level 9 Base gained +5 Special Size, +10 Standard Size, 5 Production Points, and 4050 Hull/Shield. This should be in the "Legion" section of the Forums...unless you financed the entire thing yourself... If you'd read his previous post, you'd see he discussed his legion base. |
| Mon Oct 08, 2018 2:31 am |
|
|
Joined: Tue Aug 16, 2011 3:02 pm Posts: 942 |
Still not a "personal" goal and this is a "ship" log not a "legion" log.
_________________ As of 08/07/2021 treadmillers will be ZEROED!!! |
| Mon Oct 08, 2018 2:35 am |
|
|
|
Page 4 of 9 |
[ 180 posts ] | Go to page Previous 1, 2, 3, 4, 5, 6, 7 ... 9 Next |
|
All times are UTC |
Who is online |
Users browsing this forum: No registered users and 21 guests |
| You cannot post new topics in this forum You cannot reply to topics in this forum You cannot edit your posts in this forum You cannot delete your posts in this forum |
